Cachewall
If you are receiving errors with the WHM\cPanel interfaces please run the below command to update:
yum update cachewall --enablerepo=cachewall-development
Cachewall is a feature-rich software package providing simple management of Varnish Cache, the open source high-performance HTTP accelerator developed by Poul-Henning Kamp, Varnish Software, and numerous open source contributors to their project.
The Cachewall control panel software has been created for use with cPanel on shared web hosting servers, but we hope that it is useful to others in any similar applications. Work is underway to support non-cPanel systems and alternative backends, such as LiteSpeed and Nginx.
Features include:
- Automatic setup and configuration of Varnish Cache, serving as a website-optimizing frontend for the standard cPanel hosting stack. Our customized Varnish Cache configuration is tailored to minimize disruptions to websites ("outdated pages" showing to visitors) while still providing significant optimization benefits.
- Simple configuration and management of Varnish Cache configuration files (VCL) without needing to understand or hand-edit the complex syntax.
- Easy-to-use management using the WebHost Manager (WHM) plugin and the xvctl command line utility.
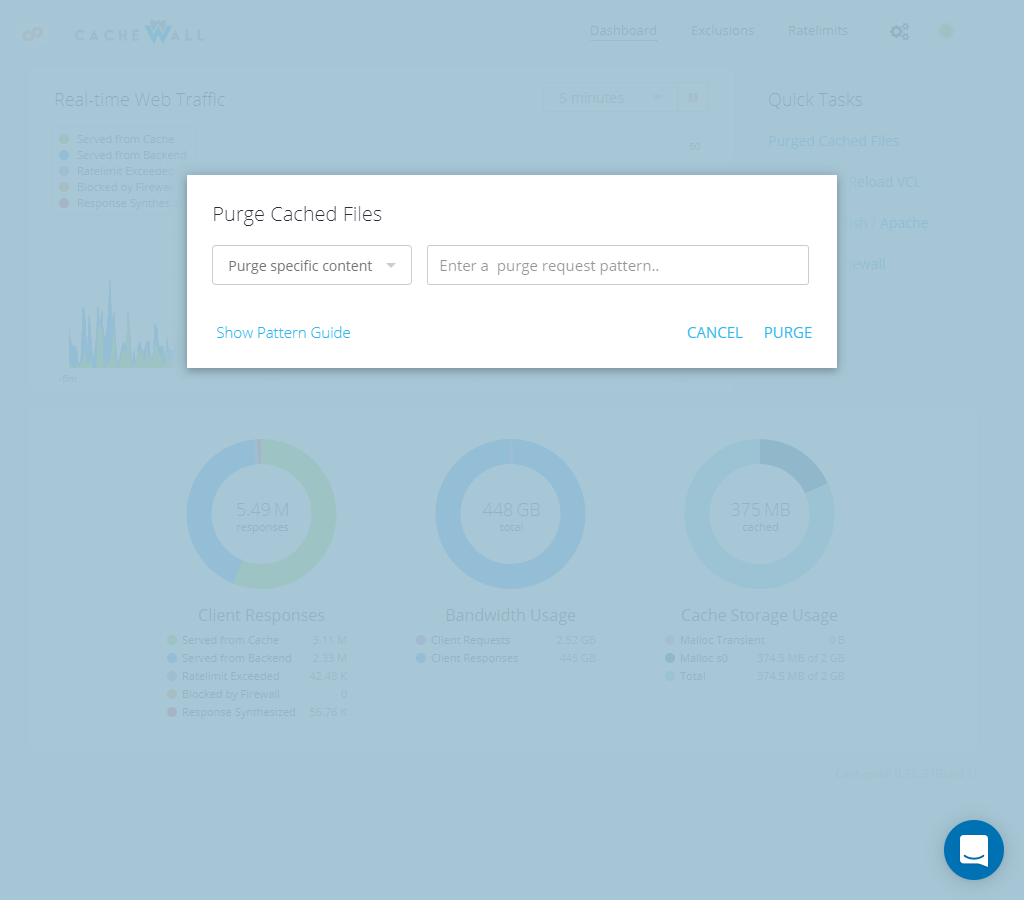
- An end-user cPanel plug-in which allows your customers to disable caching permanently or temporarily ("Development Mode"), as well as purge cached files.
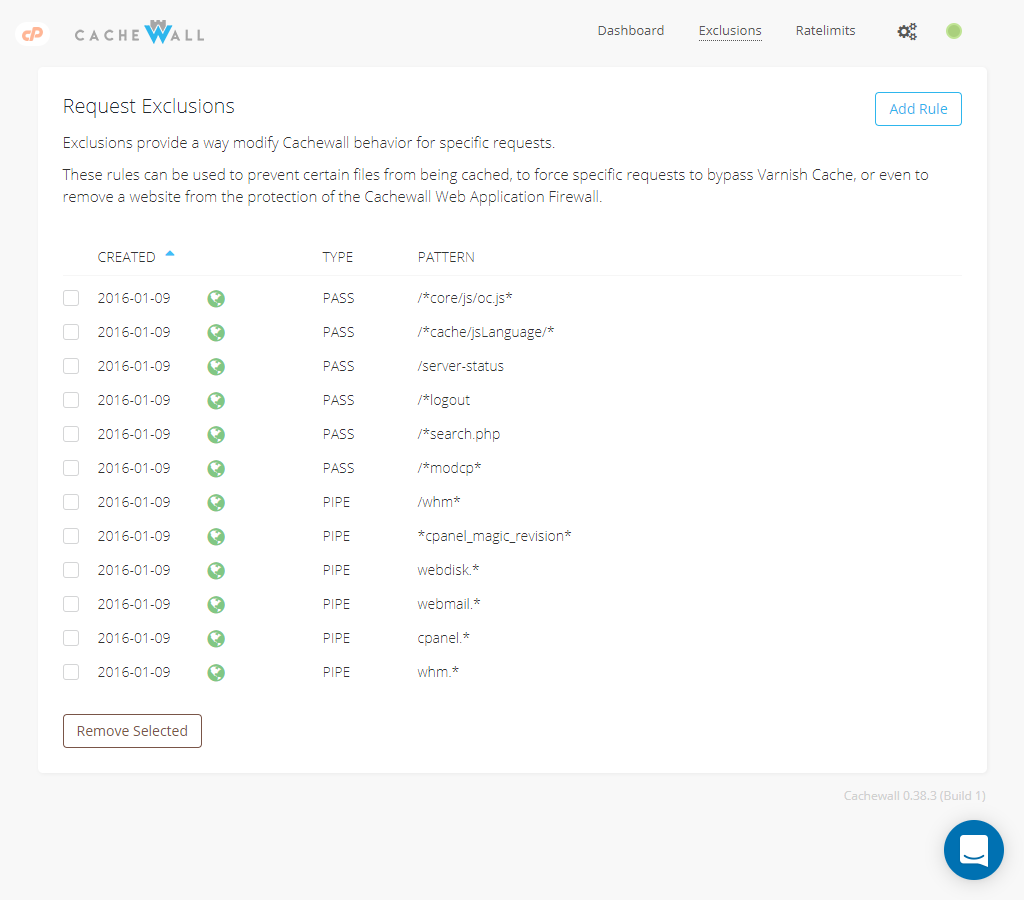
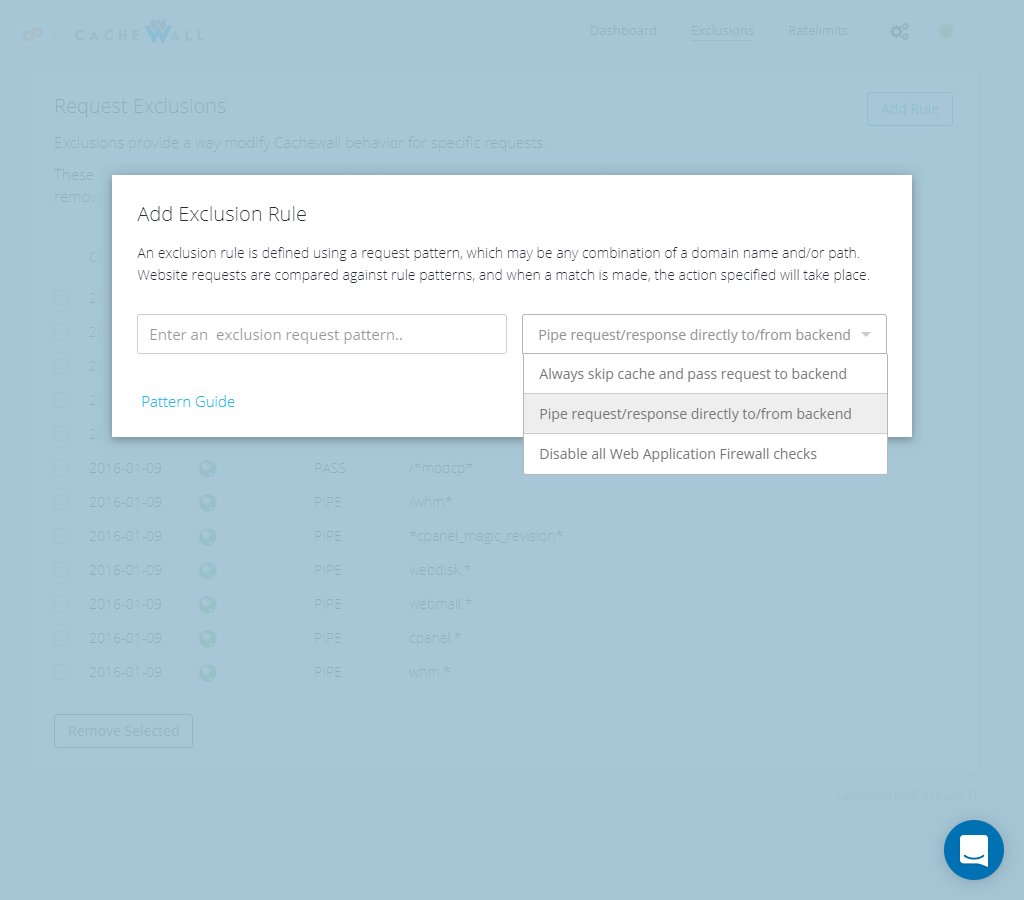
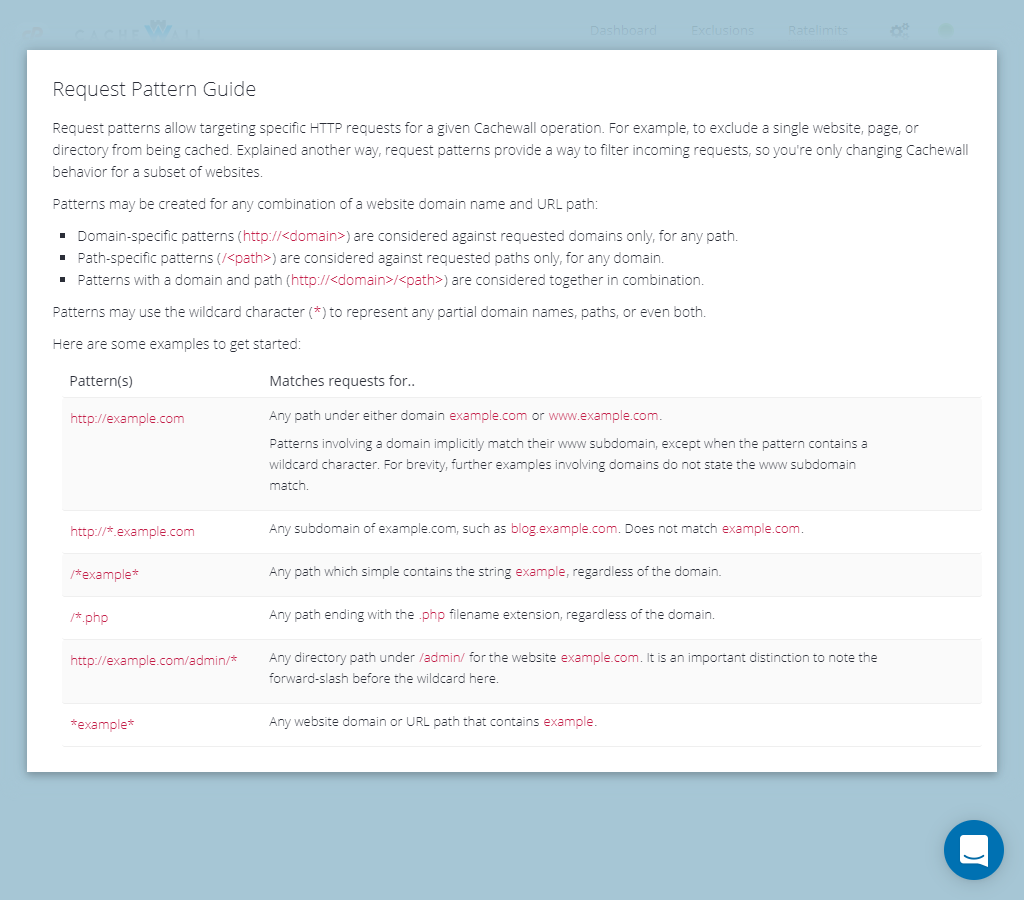
- Flexible, pattern-based exclusions to specify websites and files that shouldn't be served cached or should always be passed-through directly to Apache.
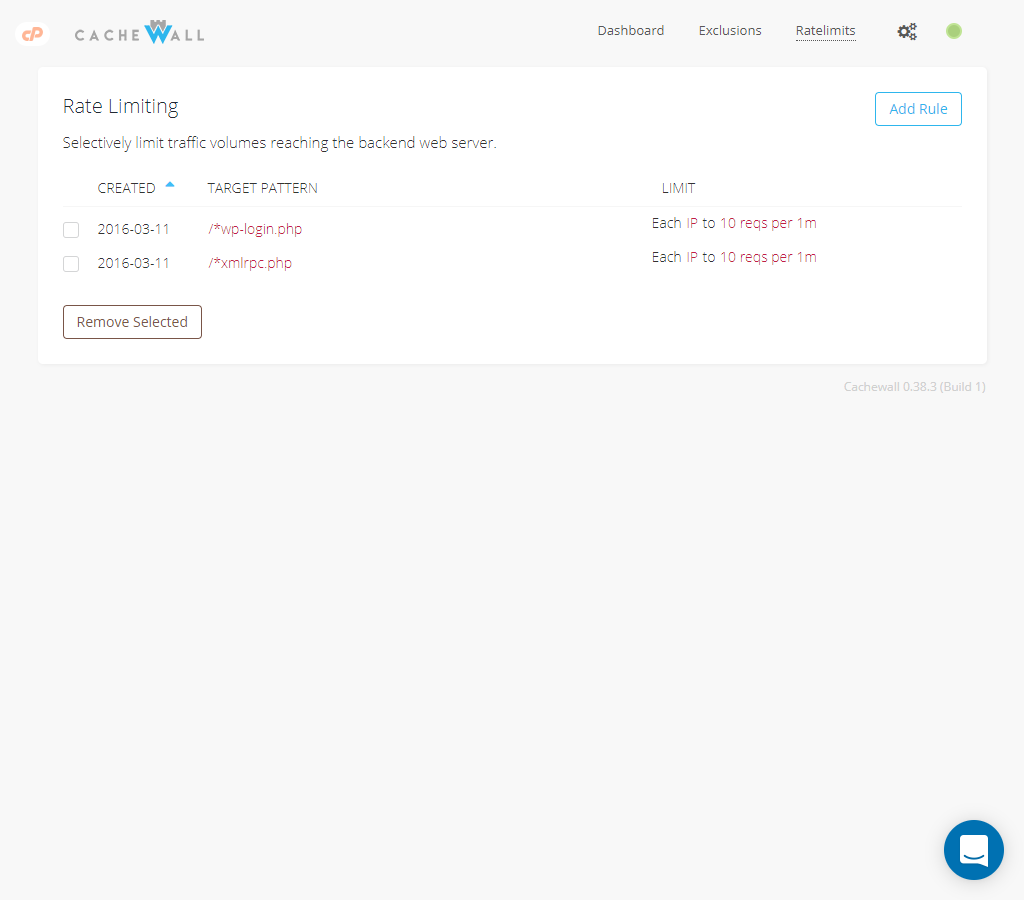
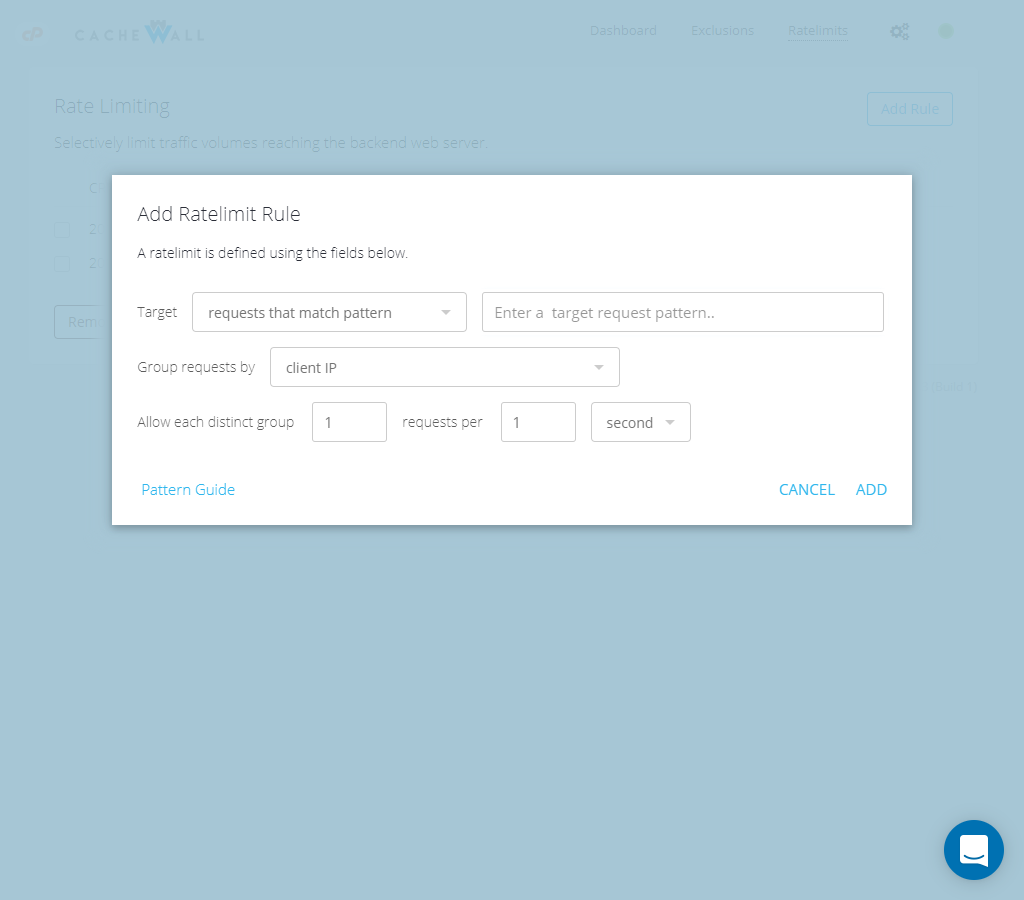
- The ability to create custom rules to rate limit website requests against high traffic volumes. Default rule set includes brute-force protection for WordPress wp-login.php, protecting your customers and reducing unnecessary CPU consumption by botnets.
- Dramatic improvement in website responsiveness across the server.
- Detailed historical traffic statistics for individual websites.
- HTTPS (TLS) traffic caching and optimization without any complex changes to your cPanel server (via Hitch).
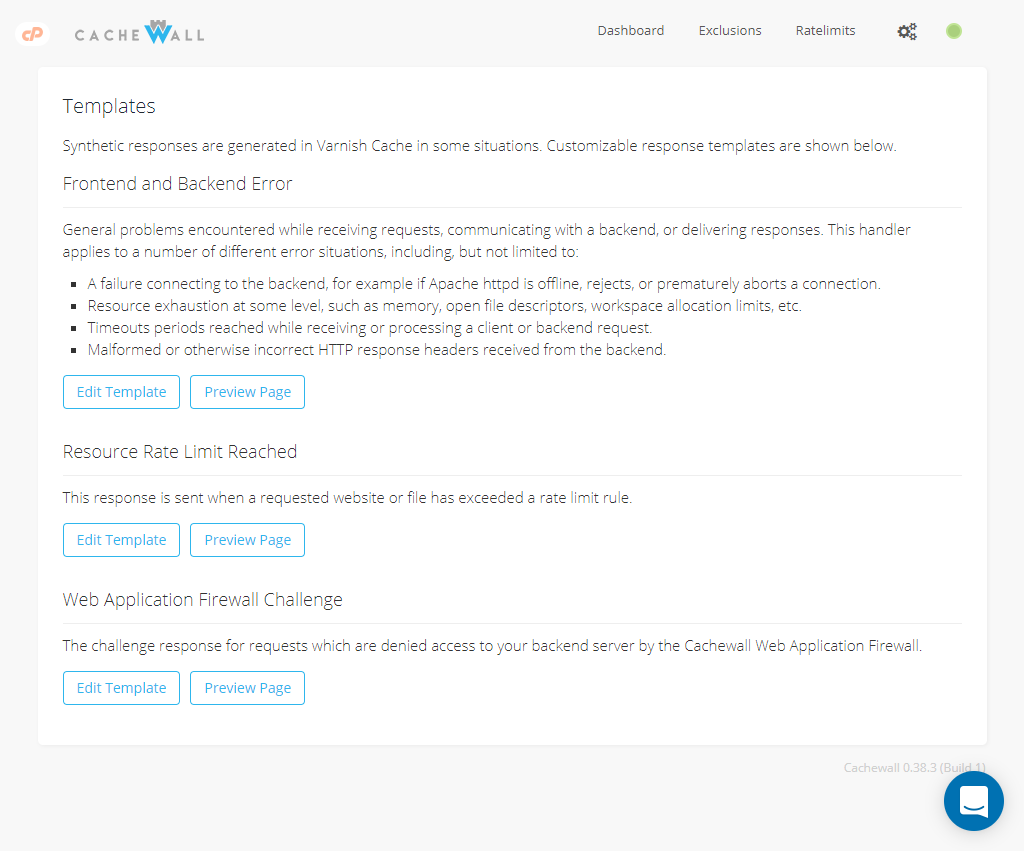
- A customizable Web Application Firewall (WAF) to filter malicious traffic before it even reaches your customer websites.
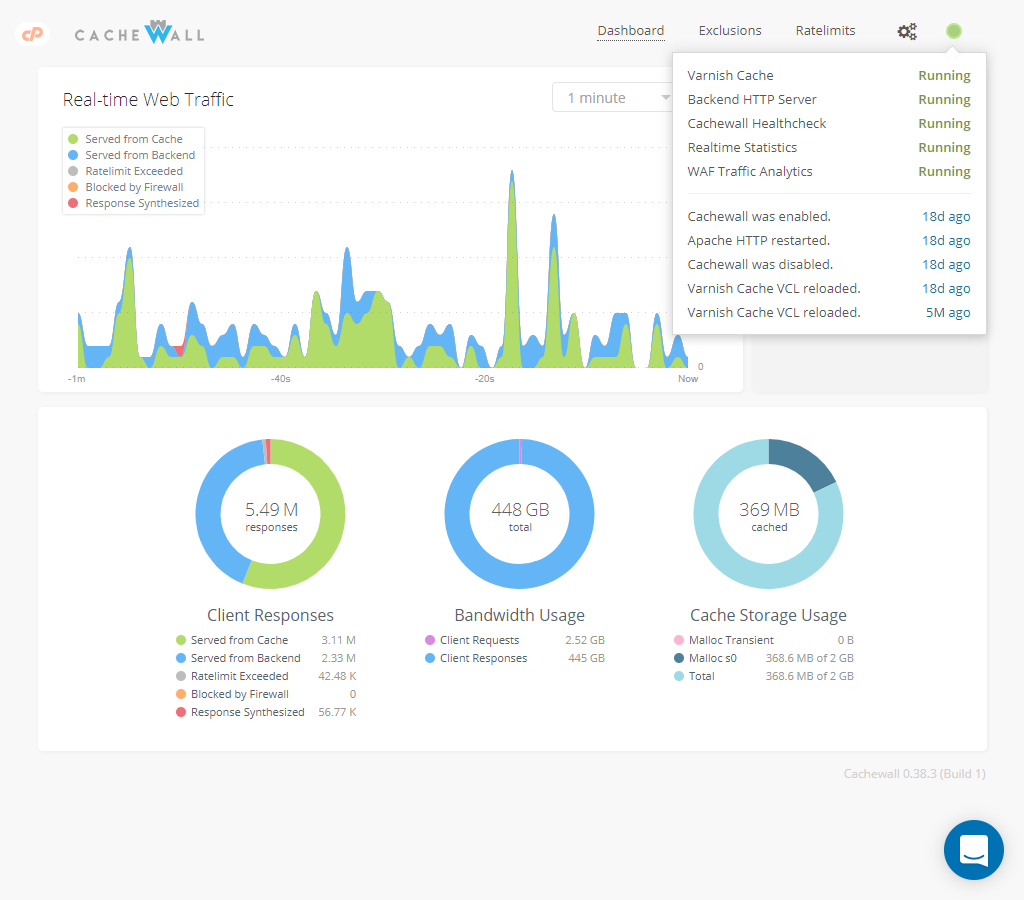
- A real-time chart of requests processed by your server (cache hits/misses) over time.
- And much more..
Cachewall is production-ready for all cPanel versions and provides an immediate, significant improvement in website performance. While it's heavily dependent on traffic characteristics, we've seen numerous cases where CPU utilization by PHP/CGI scripts is reduced by over 50% - without negatively impacting website visitors!
The Cachewall software has been under active development and used in production shared web hosting since 2014.
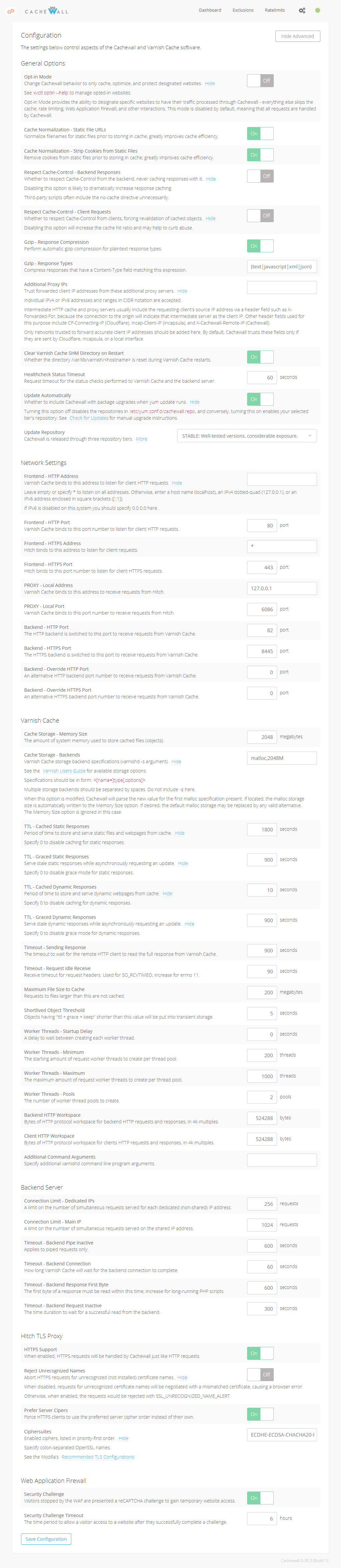
Interface Screenshots
News
We are currently providing limited support while we work on our next update. Thank you for your patience.
Current Versions:
Release 0.40.2, April 17th, 2018
Edge 0.40.4, April 19th, 2018
Changelog is available here.
Install
Cachewall is compatible with cPanel under both CentOS 6 and CentOS 7 (including CloudLinux 6 and CloudLinux 7). The software may be installed in both dedicated and virtual server environments. Cachewall works with all cPanel versions, EasyApache 3, EasyApache 4 (see Note for EA4), and LiteSpeed WebServer.
To install Cachewall, run:
rpm -ivh https://repo.cachewall.com/cachewall-release.rpm
yum install cachewall
Note for EA4: If you're using cPanel EasyApache 4 you should install the ea-apache24-devel cPanel package. This provides apxs which is necessary to configure Cachewall mod_xvarnish for visitor IP address correction. See Real Client IPs with Apache for more information.
Please get in touch if you experience any problems. We will work with you to troubleshoot and promptly issue a bugfix if necessary.
Upgrade
To upgrade Cachewall, run:
yum update cachewall
Using Cachewall
The installation provides a completely hand-free setup of your server for Cachewall and Varnish Cache.
You should now register on cachewall.com by entering your email address if you have not already done so. You will be immediately sent new account access information for the Cachewall license manager and after signing in, you can create a license key for any number of servers. There is no cost currently for using Cachewall on any number of servers, and when that changes there we will provide notification at least 2 months in advance. (Written January, 2018)
A WebHost Manager plugin is installed for management, and you may also use the xvctl utility for equivalent management functionality via the command line (see xvctl --help).
Once you have your license key, run:
/usr/local/xvarnish/bin/activate --key <license-key>
Cachewall is not enabled automatically by default. Once you're ready you can simply access the Cachewall plugin under WebHost Manager to make the web server switch. You can run this right from the command line too:
xvctl enable cachewall
xvctl enable https
During the enable process, your traditional HTTP service (Apache, LiteSpeed, etc) is configured to listen on HTTP port 0.0.0.0:82 to serve as the backend for Varnish Cache, and Varnish Cache is configured to listen on HTTP port 0.0.0.0:80. Varnish Cache receives requests and if necessary, forwards them to the HTTP backend to retrieve the response. When Cachewall HTTPS is enabled, your traditional HTTPS service is configured to listen on port 0.0.0.0:445, and Hitch is configured to replace it on HTTPS port 0.0.0.0:443. Hitch terminates TLS and proxies plaintext requests to Varnish Cache via PROXY port 127.0.0.1:6086, where the request is then sent to the HTTPS backend if necessary. These changes are reverted when Cachewall is disabled, and the involved port numbers are configurable if necessary.
Want to live on the edge? Install the latest testing release with:
yum install cachewall --enablerepo=cachewall-edge
Troubleshooting
Cachewall's xvctl utility provides the -v option to enable debug output and logging. If you're facing troubles, it's usually helpful to add this argument onto your command. You can actually specify -v multiple times to increase verbosity. For example: xvctl -vvv enable https
It's also possible to enable debug logging in the Cachewall configuration file. Edit /usr/local/xvarnish/settings and set log_level = DEBUG. You'll see debug log messages written into /var/log/xvarnish/xvarnish.log when xvctl runs. The xvhealth and xvstats service must be restarted before they'll pick up changes to log_level.
You may set LOG_ECHO=1 in your environment to enable debug logging for xvctl (export LOG_ECHO=1). Use this variable to enable debug logging for problems during installation and upgrades: export LOG_ECHO=3 yum update cachewall
Cachewall may be disabled at any time via the WebHost Manager plugin, and the disable process immediately reverts all cPanel and web service configurations to their original. If you experience a significant problem you should disable Cachewall and get in touch with our support. To immediately disable Cachewall and Varnish Cache, run:
xvctl disable cachewall
Use the revert-apache.sh shell script if xvctl is not functional:
bash /usr/local/xvarnish/bin/revert-apache.sh
Uninstall
Run the command below to fully uninstall Cachewall. Please note that we recommend disabling Cachewall but leaving it installed in the event you're experiencing a significant problem. Cachewall performs the same configuration revert during disable as it would for a full uninstall; the software shouldn't impact your service while its disabled. This helps us greatly while investigating any support help requests.
To uninstall, run:
yum remove cachewall cachewall-vmods cachewall-release varnish
Cachewall leaves some configuration files in /usr/local/xvarnish and log files in /var/log/xvarnish. If you wish to remove everything, run:
rm -rI /usr/local/xvarnish /var/log/xvarnish
Support
Please see: Cachewall Technical Support Guide
Downloads
CHANGELOG cachewall-release.rpm NEWS getting-started-readme.txt revert-apache.sh varnishlog.sh authsecret.sh cacheperf.sh